Properly sanitizing your code is just the first step in a clean workflow. To keep your project data organized, check out our JSON Formatter & Validator for debugging your API responses, or head over to our PX to REM Converter to ensure your layouts stay perfectly responsive across all devices.
To successfully unpack and format your source using the Toolbity JS Architect, follow these streamlined steps:
1. Ingest Source: Paste your minified or obfuscated JavaScript into the input terminal.
2. Configure Unpackers: For modern obfuscators, ensure "Unpack Arrays" and "Rename Hex Identifiers" are toggled on.
3. Resolve Logic: Utilize the "Simplify Expressions" feature to convert complex hex-math into readable decimal values.
4. Execute & Export: Click "Process Source Code" and use the built-in copy button to export your clean, beautified code.
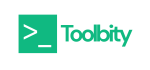
Beyond basic beautification, our JS Deobfuscator handles the heavy lifting of architectural reverse engineering:
1. Array Unpacking: We detect constant-array patterns and map indices back to their original string values.
2. Proxy Function Removal: We simplify intermediate "getter" functions that obfuscators use to hide simple logic.
3. Hex Identifier Renaming: We replace unreadable variable names (e.g., _0x4f21) with logical identifiers, making the code flow instantly recognizable.
Is this JS Deobfuscator secure?
Yes. All processing occurs locally in your browser via client-side JavaScript. Your source code is never transmitted to our servers.
Can this tool detect Malicious Payloads?
The tool itself is a de-obfuscation and analysis environment, not a virus scanner. However, it is an essential first step for malware analysts. By revealing hidden strings and unpacking arrays that typically house C2 (Command and Control) URLs or encoded binary data, analysts can quickly identify "Indictors of Compromise" (IOCs) that would otherwise be invisible to static scanners.What are Pr
Can it reverse all obfuscation?
It is optimized for the vast majority of common obfuscation patterns, including those used by professional-grade script scramblers.
How does the tool handle Control Flow Flattening?
Control flow flattening is a technique where linear code is broken into a central "dispatcher" (often a large switch statement) inside a loop. This makes the logic difficult to follow sequentially. By using the Simplify Expressions and Beautify toggles, our tool reorganizes the structure, allowing security researchers to more easily identify the underlying state-machine logic and restore the original program flow.
Does it work with SRI?
Absolutely. We recommend using this tool to audit a script's behavior before using our SRI Hash Generator for deployment.
What is the difference between Minification and Obfuscation?
While both processes make code harder to read, their intent is different. Minification is a performance-focused process that removes whitespace, comments, and shortens variable names to reduce file size. Obfuscation, however, is a security-focused transformation designed to hide the logic and intent of the code. Our JS Deobfuscator handles both, stripping away the complexity of scrambled identifiers while also pretty-printing minified "one-liners."
In the 2026 landscape of web security and malware analysis, interpreting minified or "scrambled" code is a critical skill. Our JS Deobfuscator is a professional-grade utility engineered to reverse complex protection layers and restore total legibility to your scripts. Whether you are auditing a third-party script for an SRI Hash or debugging your own minified production build, this tool provides a high-fidelity environment to analyze your JavaScript source safely and effectively.
While minification is a standard practice for performance, intentional obfuscation is often used to hide logic, mask malicious redirects, or protect proprietary algorithms. This tool provides a high-fidelity, client-side environment to analyze JavaScript source code safely and effectively, ensuring that what you see is exactly what your browser executes.
Professionals utilize our JS Deobfuscator as a vital security instrument to transform "black-box" scripts into transparent, auditable logic. By unpacking scrambled production builds, experts can perform deep-dive supply chain audits before deploying an [SRI Hash], accelerate malware analysis during incident response, and recover lost legacy source code. Crucially, our tool operates entirely client-side, ensuring total data sovereignty by processing sensitive proprietary code without it ever leaving your local environment.